Generate Ssh Key Mac For Aws
Posted By admin On 11.12.20Security can be easily overlooked when building a product, especially when working with an outsourced engineering team. You want to trust them, so you give them access to your servers. But then you discover fraudulent activity, and, well, you start to panic.
Use the ssh-keygen command to generate SSH public and private key files. By default, these files are created in the /.ssh directory. You can specify a different location, and an optional password (passphrase) to access the private key file. If an SSH key pair with the same name exists in the given location, those files are overwritten. How to Create SSH Keys with OpenSSH on MacOS or Linux Validated on 28 August 2019 • Posted on 19 June 2018 DigitalOcean Droplets are Linux-based virtual machines (VMs) that run on top of virtualized hardware. Each Droplet you create is a new server you can use, either standalone or as part of a larger, cloud-based infrastructure. Jan 24, 2017 This video describes the workflow for generating RSA Key Pairs on a Mac device using JumpCloud. The process can be replicated on a Linux device. SSH Key Management for AWS. How to Generate. Touch /.ssh/authorizedkeys C. Fix the permissions: chmod 600 /.ssh/authorizedkeys D. Copy AWS Key to that file: cp AWSkey.text sam/.ssh/authorizedkeys #You would have saved this SSH key earlier when creating the EC2 instance. Then test the ssh to AWS Linux server - you will see this error: ssh -i./authorizedkeys root@ec2-54-76-176-29.ap-southeast-2.compute.amazonaws.com Please login as. Login to the AWS EC2 console and select Key Pairs in the left sidebar On the next page, click the Create Key Pair button Give the new key a name, then click the create button Download the new key, and then chmod it to 0666.
In hindsight, you realize you never should have shared your Secure Shell (SSH) key, instead storing it in a vault with restricted user access. If, however, someone has a private SSH key to your Amazon Web Services (AWS) Elastic Compute Cloud (EC2) instance and you’re worried about a malicious attack, you have two options to revoke their access:
- Create a new key-pair in the AWS console and boot up a new instance (assuming the attacker is removed from IAM users). This requires configuring the instance, which can be time-consuming — especially when you have several of them.
- Replace the public key in ~/.ssh/authorized_keys on your existing instance so the attacker can no longer unlock it with their private key.
Here’s a summary of how to replace the keys mentioned in option No. 2 above:
(For more, DigitalOcean has a great tutorial on setting up SSH keys.)
- On your local machine in the terminal, generate a new key pair:
ssh-keygen -t rsa - When prompted to save the file, hit Enter for the default location or choose your own path.
- When prompted for a passphrase, you can leave the field empty. Although it does not hurt to have more security, if the key pair is used elsewhere for CI or automation, you will need to leave the passphrase empty — machines cannot guess passphrases.
- Copy the public key you just saved on your machine to your EC2 authorized keys file:
cat ~/.ssh/id_rsa.pub ssh user@123.45.56.78 'mkdir -p ~/.ssh && cat >> ~/.ssh/authorized_keyswhere ~/.ssh/id_rsa.pub is the new key on your machine and user@123.45.56.78 is the username and IP address of your EC2 instance. - At this point, your new public key should be on your EC2 instance in the authorized_keys file, and all you have to do is remove the old one. Make sure you can SSH into your EC2 instance with the new key first.
- Once you’re in, you can remove the old key using
vim ~/.ssh/authorized_keysJust go to the line with the old key and remove it:ddNote: If you tried editing the file and didn’t save it, or the connection was interrupted, an .authorized_keys.swp file will be created, and the next time you try to edit your authorized_keys, you will get a nasty message. Just delete the .swp file, and you should be good to edit. - Save the file.
Make sure to update the key if you’re using it elsewhere, like on a continuous integration (CI) server. Otherwise you’ll be scratching your head when none of your builds are working.
You generate an SSH key through macOS by using the Terminal application. Once you upload a valid public SSH key, the Triton Compute Service uses SmartLogin to copy the public key to any new SmartMachine you provision.
Joyent recommends RSA keys because the node-manta CLI programs work with RSA keys both locally and with the ssh agent. DSA keys will work only if the private key is on the same system as the CLI, and not password-protected.
About Terminal
Terminal is the terminal emulator which provides a text-based command line interface to the Unix shell of macOS.
To open the macOS Terminal, follow these steps:
- In Finder, choose Utilities from the Applications folder.
- Find Terminal in the Utilities listw.
- Open Terminal.

The Terminal window opens with the commandline prompt displaying the name of your machine and your username.
Generating an SSH key
An SSH key consists of a pair of files. One is the private key, which should never be shared with anyone. The other is the public key. The other file is a public key which allows you to log into the containers and VMs you provision. When you generate the keys, you will use ssh-keygen to store the keys in a safe location so you can bypass the login prompt when connecting to your instances.
To generate SSH keys in macOS, follow these steps:
Enter the following command in the Terminal window.
This starts the key generation process. When you execute this command, the
ssh-keygenutility prompts you to indicate where to store the key.Press the ENTER key to accept the default location. The
ssh-keygenutility prompts you for a passphrase.- Type in a passphrase. You can also hit the ENTER key to accept the default (no passphrase). However, this is not recommended.
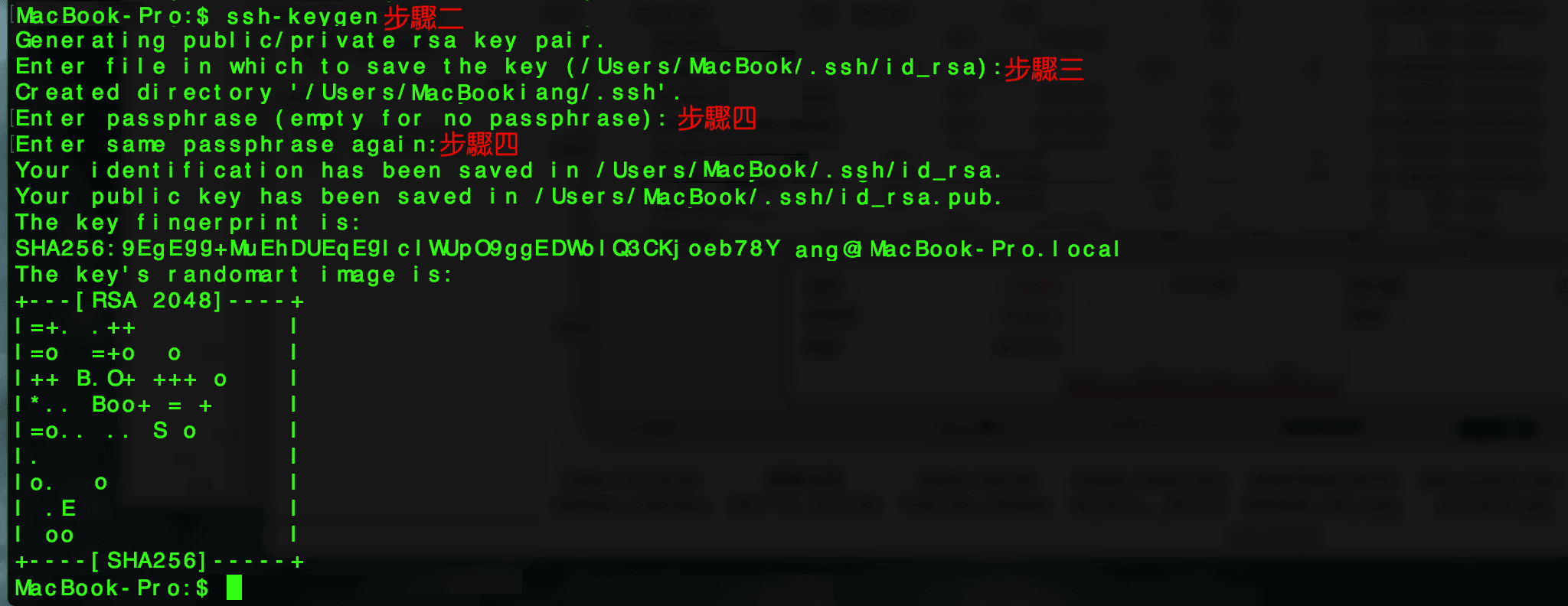
You will need to enter the passphrase a second time to continue.
After you confirm the passphrase, the system generates the key pair.
Your private key is saved to the id_rsa file in the .ssh directory and is used to verify the public key you use belongs to the same Triton Compute Service account.
Generate Ssh Key Mac For Aws Pc
| Never share your private key with anyone! |
|---|
Your public key is saved to the id_rsa.pub;file and is the key you upload to your Triton Compute Service account. You can save this key to the clipboard by running this:
Importing your SSH key
Now you must import the copied SSH key to the portal.
- After you copy the SSH key to the clipboard, return to your account page.
- Choose to Import Public Key and paste your SSH key into the Public Key field.
- In the Key Name field, provide a name for the key. Note: although providing a key name is optional, it is a best practice for ease of managing multiple SSH keys.
- Add the key. It will now appear in your table of keys under SSH.
Troubleshooting
You may see a password prompt like this:
This is because:
- You did not enter the correct passphrase.
- The private key on your Macintosh (
id_rsa) does not match the public key stored with your Triton Compute Service account. - The public key was not entered correctly in your Triton account.
What are my next steps?
Right in the portal, you can easily create Docker containers, infrastructure containers, and hardware virtual machines.
Mac Os Generate Ssh Key
In order to use the Terminal to create instances, set up triton and CloudAPI as well as the triton-docker commandline tool. Windows 7 activation home premium key generator.